Anthropic Mythos’ ability to autonomously identify and exploit system vulnerabilities have raised important questions regarding cybersecurity controls, operating approaches, and the effectiveness of cybersecurity programs and associated investments.
While the model’s ability to identify and exploit security vulnerabilities autonomously — at scale and with multi-step reasoning — is significant, the core phases (reconnaissance, discovery, assessment, and exploitation) remain consistent. The principal change is the increased speed of execution and the consolidation of extensive knowledge within a single operational framework.
For leaders overseeing cybersecurity programs, the implications are clear: exposure windows must be reduced, containment strategies strengthened, and incident response protocols prepared for higher-frequency, higher-volume events. In essence, Artificial intelligence is accelerating the interval between vulnerability disclosure and exploitation, while also increasing the prevalence of browser- and identity-based attacks.
This briefing presents a recommended strategy emphasizing measurable risk reduction, encompassing both “immediate” and “mid-term” actions. It highlights essential, proven controls that enable organizations to assess their risk posture and prioritize mitigation efforts in response to this evolving landscape.
Understanding the Key Changes in the Threat Landscape
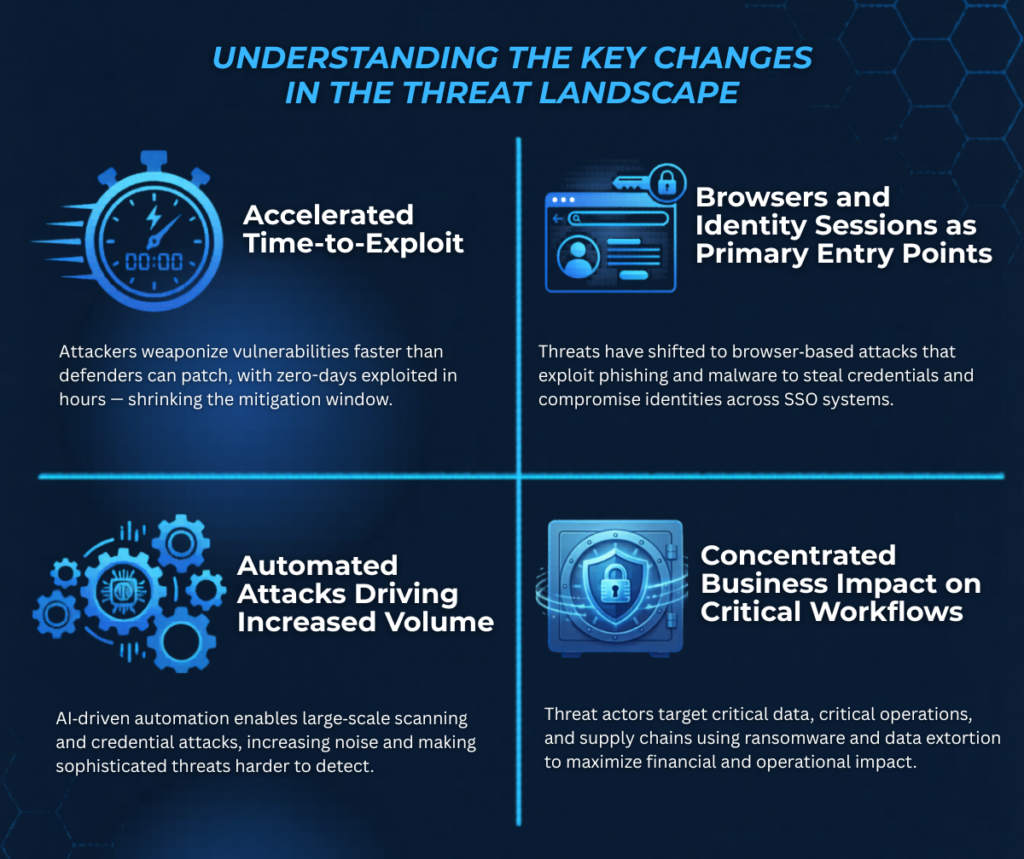
Accelerated Time-to-Exploit
The window between vulnerability disclosure and exploitation has shortened materially, with adversaries increasingly measuring time-to-exploit in days — and, in some cases, hours. This pace renders traditional patch cycles and change-management windows less effective, creating a growing misalignment between legacy processes and current threat conditions.
Browsers and Identity Sessions as Primary Entry Points
Browsers and identity sessions have become adversaries’ primary gateways into systems. By compromising client-side environments and stealing authentication tokens, adversaries can bypass many existing perimeter-security investments, shifting attacks away from traditional network defenses.
Automated Attacks Driving Increased Volume
The use of automation has enabled adversaries to probe and re-probe a greater number of targets continuously. This persistent activity results in a higher operational burden for IT and security operations teams, as they must contend with an ever-expanding attack surface and faster attack cycles.
Concentrated Business Impact on Critical Workflows
The consequences of these evolving threats are most acute in key business workflows, particularly those involving privileged access, customer-facing web applications and APIs, and high-value data stores. These areas require explicit protection and rigorous validation, as they represent the “crown jewels” of organizational assets and are at heightened risk of compromise.

Recommended Cybersecurity Control Hygiene Actions and Adjustments
Stabilize Your Exposure— Immediate Term (0–60 days)
- Implement an emergency patch protocol (CIO/CTO oversees execution, CISO prioritizes): Define distinct service-level agreements for internet-facing assets, browsers/endpoints, edge/VPN, and identity infrastructure. Allow out-of-band changes for vulnerabilities that are actively exploited or assessed as highly credible.
- Harden browsers and endpoints: Deploy managed browser solutions, mandate prompt automatic updates, enforce extension allowlists, and apply endpoint attack surface reduction policies.
- Reduce identity takeover risk: Extend phishing-resistant multi-factor authentication to privileged users, strengthen conditional access controls, shorten session duration for high-risk activities, and assess and restrict token issuance pathways.
- Strengthen containment to minimize blast radius: Restrict outbound internet traffic from servers where feasible, reinforce segmentation around critical applications and data, and implement DNS/proxy controls to impede automated attacks and data exfiltration.
- Reduce unnecessary attack surface: Decommission obsolete services and administrative interfaces and apply least privilege principles rigorously to administrative and service accounts.
- Validate detection and response readiness: Confirm completeness of identity, endpoint, web application firewall (WAF), and DNS logs; tune alerting for anomalous authentication behavior, token-theft indicators, and rapid exploitation attempts; and verify that on-call escalation procedures are current and unambiguous.
Operationalize Continuous Control Validation — Short Term (60–120 days)
- Prioritize vulnerability management by exploitability and business impact: Increase scanning frequency for internet-exposed assets and establish clear ownership and remediation protocols for vulnerabilities that are reachable, exploitable, and high risk.
- Continuously validate security controls: Run targeted purple-team exercises that simulate realistic attack paths (e.g., browser compromise leading to token theft, privilege escalation, and data access), and close identified gaps through named accountable owners.
- Strengthen standards for customer-facing applications and APIs: Reinforce software development lifecycle checkpoints with static and dynamic analysis and dependency/SBOM scanning, and implement practical API protections such as rate limiting, bot mitigation, and enhanced web application firewall (WAF) configurations.
- Reinforce identity as the primary control plane: Expand privileged access management and just-in-time administration, segregate administrative workstations, review OAuth/OIDC consent settings regularly, and reduce high-risk application permissions.
- Protect critical data pathways: Refine classification and access controls for sensitive repositories, strengthen encryption and key-management practices, and deploy egress monitoring and data loss prevention controls where they demonstrably reduce risk.
Build Durable Resilience (aka, Governance, Supply Chain, and AI-Use Controls) — Mid Term (120–240 days)
- Strengthen third-party and supply-chain assurance: Establish access controls, enable auditability, implement abuse monitoring, and define incident-notification service-level agreements for critical vendors — particularly those providing security, identity, and AI services.
- Govern AI tool usage as a privileged capability: Define approved use cases, require strong authentication and least privilege, apply prompt and data controls, and mandate comprehensive audit logging — restricting access to sensitive or regulated data unless expressly authorized.
- Modernize assurance testing protocols: Expand red- and purple-team scenarios to include rapid vulnerability chaining and large-scale browser-to-identity takeover paths.
- Expand and operationalize network and application segmentation: Use segmentation to limit lateral movement by separating workloads, enforcing least privilege access, and controlling internal traffic. Establish security zones to make broad compromise more difficult and to improve detection.
- Prepare for high-velocity incidents: Run executive and operational tabletop exercises focused on “zero-day plus browser compromise” and “identity takeover at scale,” emphasizing token revocation, privileged-access termination, and rapid isolation procedures.

Final Thoughts on AI Security
The fundamentals have not changed: reduce exposure, limit blast radius, and detect and respond quickly. What has changed is the pace. AI-driven automation is compressing the interval between discovery and impact and will continue to strain traditional change-control and patch cycles. Organizations that perform best in this environment will not “out-tool” the threat; they will out-execute it through clear ownership, rapid decision rights, and a disciplined weekly operating cadence tied to a small set of leading indicators. If we consistently shorten the patch-and-contain cycle and harden identity pathways, we materially improve the odds, even as adversary automation accelerates.
As a closing note, it is important to understand that AI security should be a shared responsibility within an organization, not just handled by the CISO. The CTO, CIO, and executive leadership all play roles in shaping systems and infrastructure, affecting how AI risks are managed. As AI is deployed across applications and platforms, its security requires coordinated oversight: the CISO sets protocols, the CTO/CIO maintains secure design, and leaders provide resources. Treating AI security as an enterprise-wide duty is crucial to managing complex, fast-evolving threats.
About the Author
Georgios designs and implements comprehensive cybersecurity programs for ERMProtect clients and helps them integrate best-in-class security technologies into their IT environments. He has large-scale programs at Norwegian Cruise Line Holdings, Sony Electronics Latin America, and ILG, Inc. From 2005 to 2013, he served as a Director of IT Security at ERMProtect.