Count the Phish: Macy's Black Friday
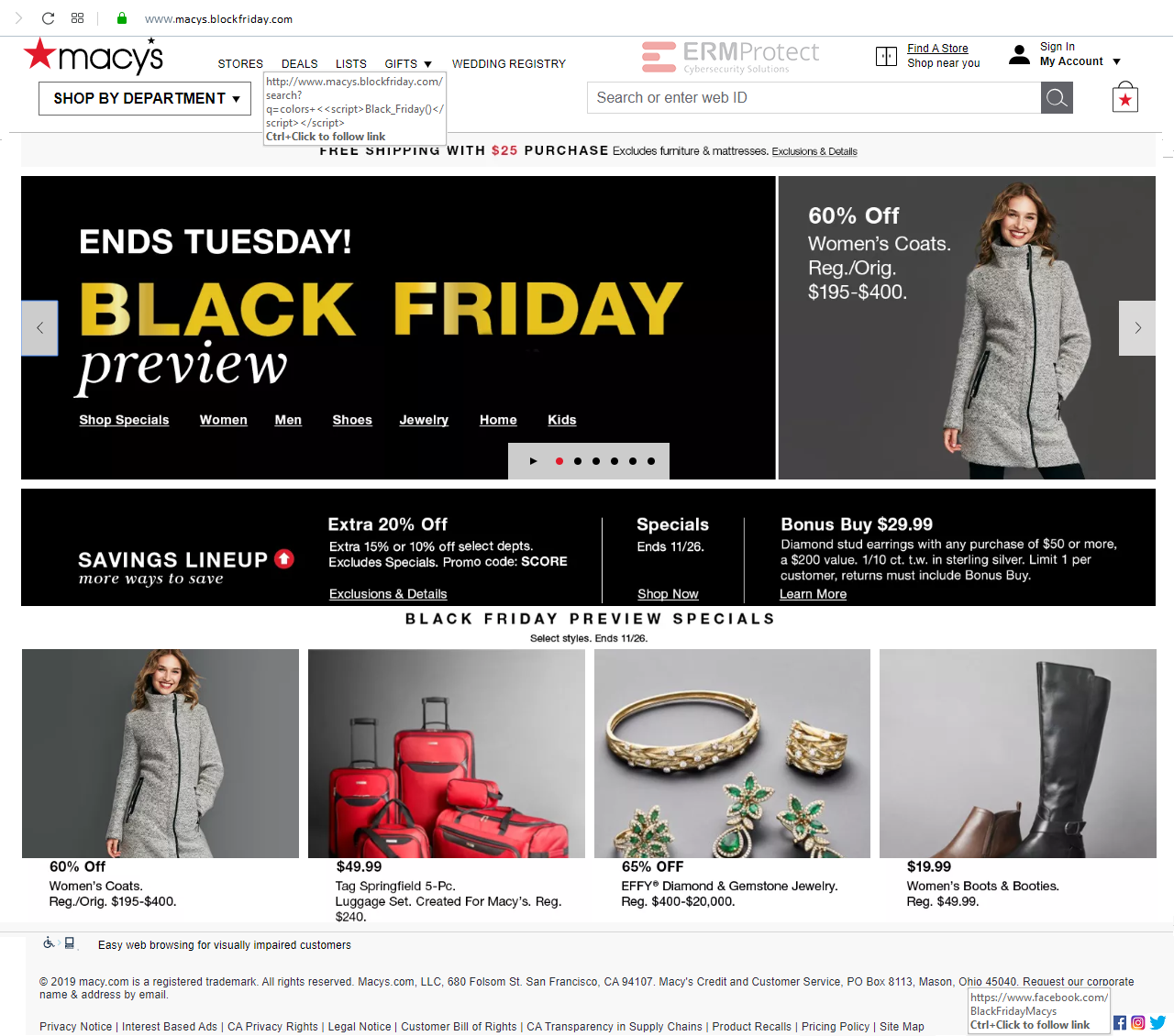
The webpage below contains one or more red flags that makes it a phishing site. How many do you count?
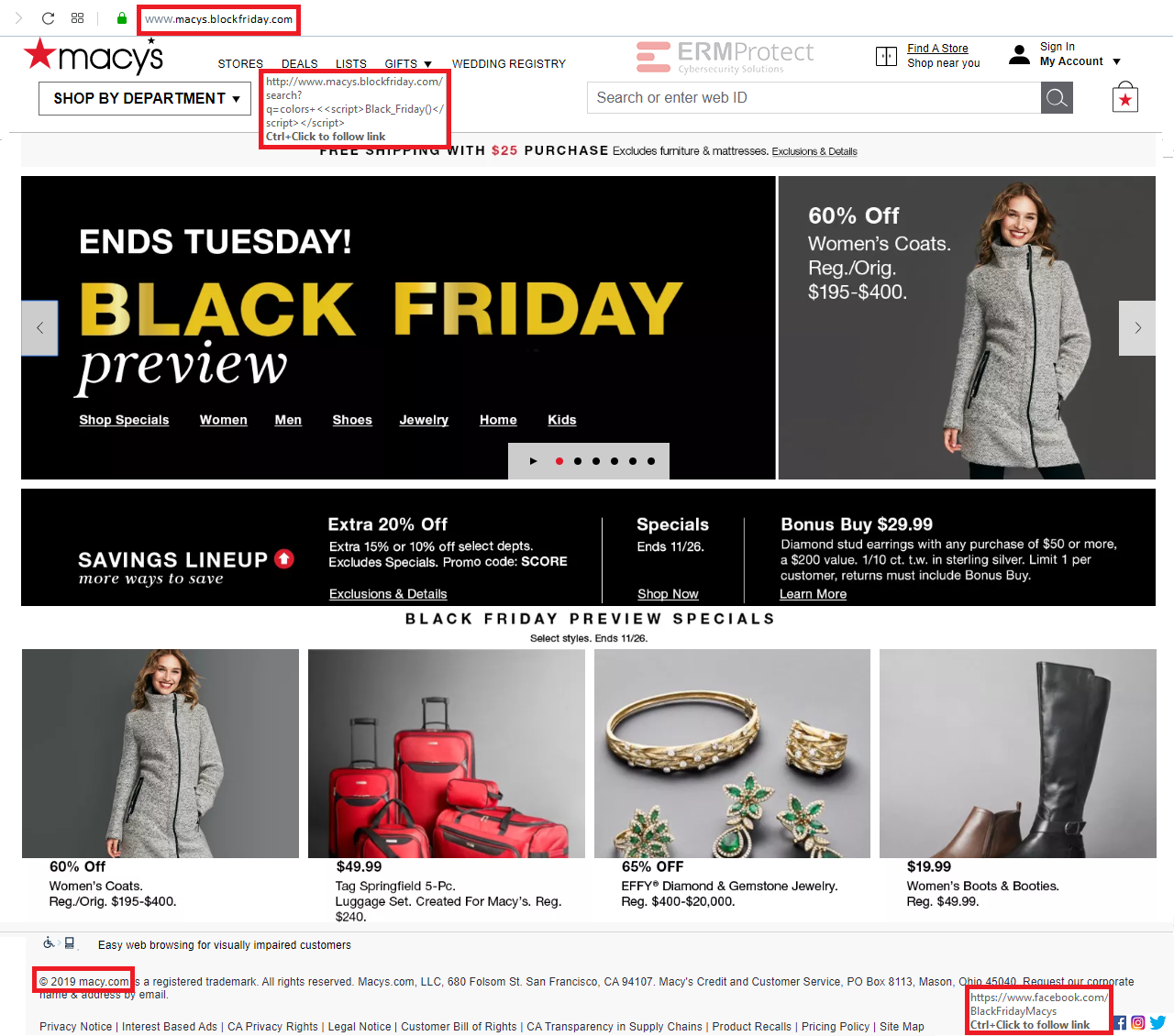
Answer: There are 4 red flags. Let’s take a look.
Phishing details:
- The first red flag is the phony URL. The actual “macys.com” domain is not the one being used here. Instead it’s “macys.blockfriday.com.” You could fall for it because you’re assuming that they may have set up a separate site specifically for Black Friday. But then why would a reputable organization like Macy’s go with a domain like “blockfriday.com”? This is clearly a domain setup by malicious phishers.
- The hyperlink for “DEALS” actually carries what is known as, a cross-site scripting attack. When the button is clicked, a new page will be loaded and this page will cause the browser to execute the script that you see in the URL called “Black_Friday().” This is most likely a malicious script. Plus, you can see again that the domain is still the phishy one from #1 above.
- The next red flag is the result of a sloppy hacker at work. If you see the copyright notice at the bottom of the page, it says “© 2019 macy.com” instead of “© 2019 macys.com.
- The last red flag is the Facebook hyperlink in the social media buttons at the bottom of the page. That’s not Macy’s Facebook page. Often times, hackers will try to lead you to other sites, including well-known social media sites, where they’ve planted malicious scripts or other such malicious ploys.

Get a curated briefing of the week's biggest cyber news every Friday.

Turn your employees into a human firewall with our innovative Security Awareness Training.
Our e-learning modules take the boring out of security training.
Intelligence and Insights

Are You Prepared for an AI-Powered Cyber Attack?
The question is no longer whether AI will impact cybersecurity, but whether organizations are prepared for the reality of AI-powered cyberattacks …

AI Privacy Risks
Users face a range of privacy concerns with AI – from models training on sensitive user data to attackers using AI tools to study their targets …

The Risk of the AI Notetaker
While AI notetakers can enhance efficiency, their adoption introduces serious risks for organizations, mainly surrounding data privacy, regulatory compliance, reputational harm, and AI security …