Spot the Phishing Attempt - Government Imposters
The images displayed below are a combination of phishing and real emails depicting government imposter scams. Spot The Phish! Click on the images to zoom in.
Spoiler Alert: Answers are below.
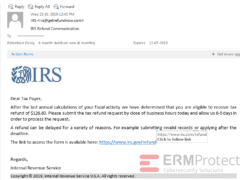
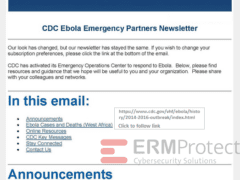
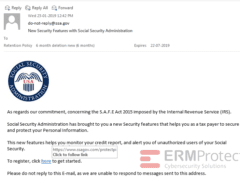
Image 2 is the only real one. And the rest are attempted phishing attacks. Take a look below as we’ve highlighted all the phishes…
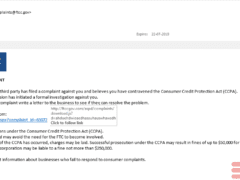
Image 1 details: The real IRS does not send emails to refund payment. Also, the real IRS does not initiate contact with you via email. The email is from [email protected], which is a spoofed email address. The sender is trying to create urgency by asking to send the refund request by close of business hours on the same day. Lastly the link to access the form, when hovered over, shows the fake site to which the user will be redirected.
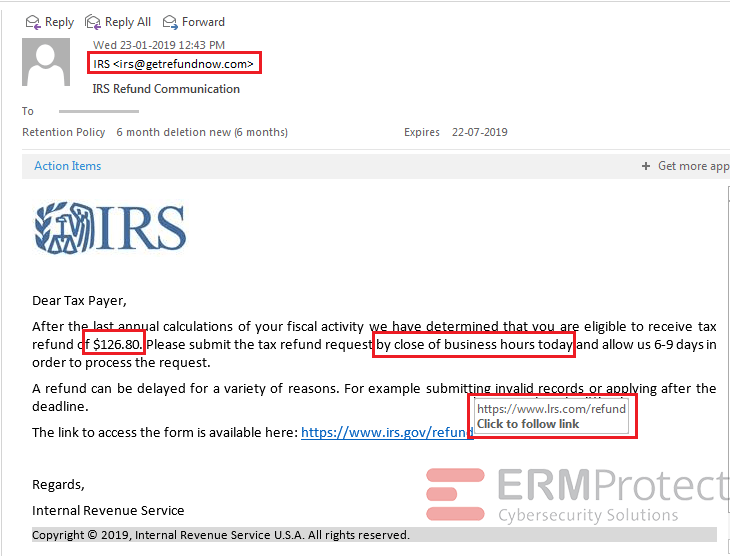
Image 2 details: Typical link checks in this email will tell you that they indeed take you to the cdc.gov domain. It appears to be a newsletter from the Center for Disease Control and Prevention (CDC). Tip: In cybersecurity, always check multiple links in the email instead of just one or two. That way, you’re doubly sure.
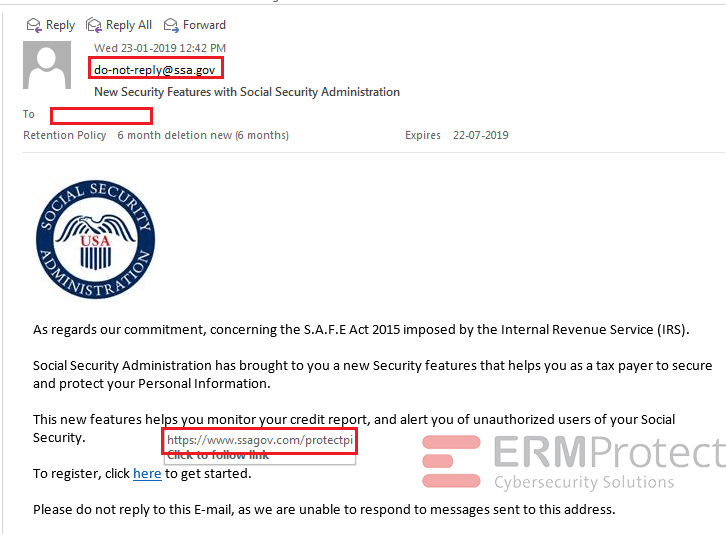
Image 3 details: The “FROM” address is a phishing email address impersonating “ssa.gov.” When you hover over the URL you’re told to click on, you see the link goes to an unrelated “.com” instead of “ssa.gov” site. Also, the “TO” field is empty.
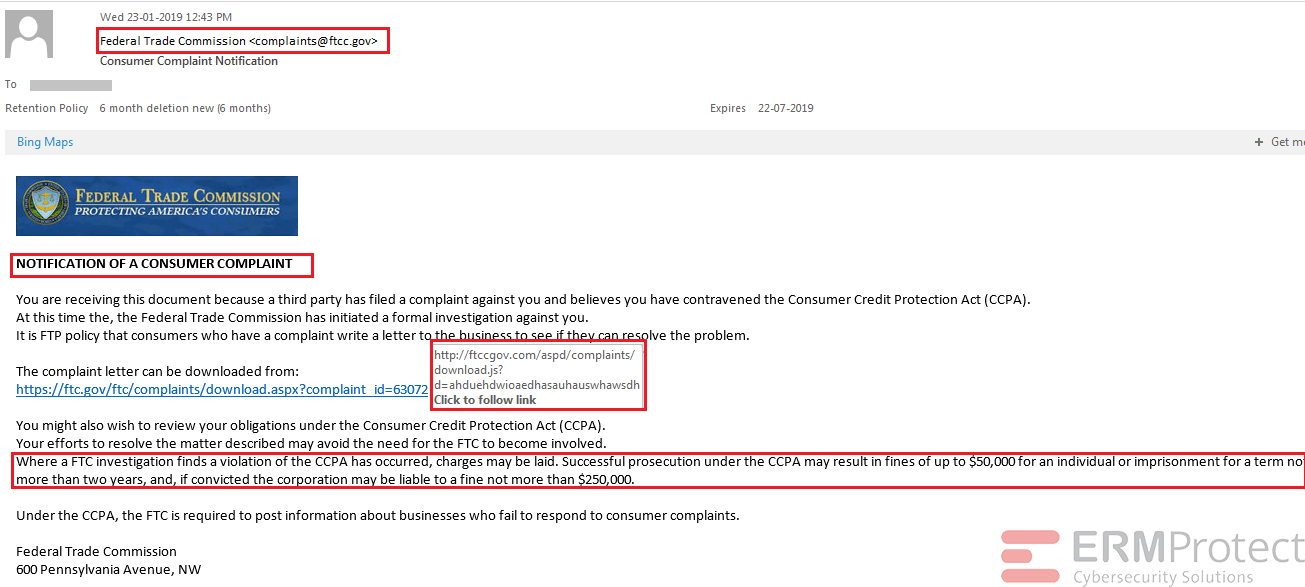
Image 4 details: The email appears to be coming from an email address [email protected], which is a fake one. In this phishing attack, the email is trying to create a sense of anxiety for the user with the heading “Notification of a consumer complaint.” Also, the link to download the form when hovered over shows an unrelated site “ftccgov.com” along with a “download.js” file which looks like a script will run when the user clicks on the link. Lastly, the phishing email tries to create fear in the user by warning about the violation, fines, or imprisonment.

Get a curated briefing of the week's biggest cyber news every Friday.

Turn your employees into a human firewall with our innovative Security Awareness Training.
Our e-learning modules take the boring out of security training.
Intelligence and Insights
Aligning Your Incident Response Plan with NIST SP 800-61 Rev. 3

CEO Checklist: How To Know If Your Organization Is Cyber Secure